A Global Ransomware Attack
The single biggest ransomware attack was launched this July by a Russian-linked gang. The gang essentially used a tool that helps protect against malware to spread it globally.
There were thousands of organizations, large firms that remotely manage the IT infrastructure of others were infected in at least 17 countries in Friday’s assault.
The name of the gang which launched this attack is called REvil. REvil is best known for extorting 11$ million from the meat processor JBS last month. REvil was seeking 5$ million payouts from the so-Called managed service providers that were its principal downstream targets in this attack, apparently demanding much less just 45000$ from their afflicted customers.
A few weeks back, it offered on its dark web site to make available a universal decryptor that would unscramble all affected machines if it’s paid 70$ Million in cryptocurrency. Some think it’s their PR stunt, while others think it indicates the criminal has more victims than they can manage.
Sweden’s government has become transparent about the situation and has informed that their grocery chain, Swedish pharmacy chain, gas station chain, state railway chain, and public broadcaster SVT were hit.
What is ransomware?
Ransomware is a type of malware that specializes in the encryption of files and drives.
In what has become one of the most severe and serious security problems modern businesses now face, ransomware is used by threat actors worldwide to hijack systems and disrupt operations.
Once a victim’s system or network has been encrypted, cybercriminals will place a ransom note on the system, demanding payment in return for a decryption key (which may, or may not, work).
Today’s ransomware operators may be part of Ransomware-as-a-Service (RaaS) when they ‘subscribe’ to access and use a particular type of ransomware. Another emerging trend is double extortion, in which a victim will have their information stolen during a ransomware raid.
If they refuse to pay up, they may then face the prospect of their data being sold or published online.
The ransomware attack, explained using Kaseya’s case
What is Kaseya ?


Kaseya‘s international headquarters is in Dublin, Ireland, and the company has a US headquarters in Miami, Florida. The vendor maintains a presence in 10 countries.
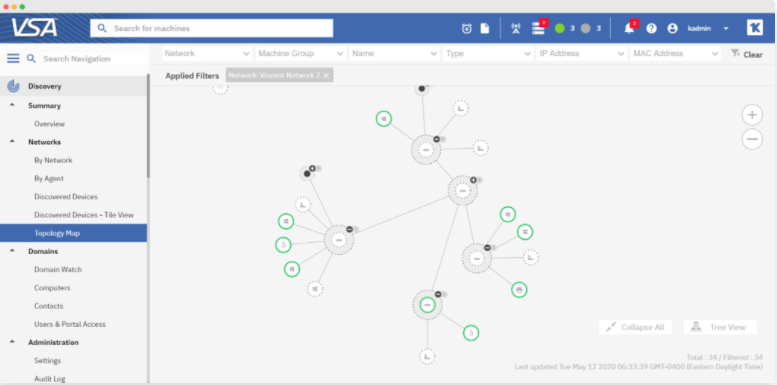
Kaseya provides IT solutions including VSA, unified remote monitoring, and management tool for handling networks and endpoints. In addition, the company provides compliance systems, service desks, and a professional services automation platform.
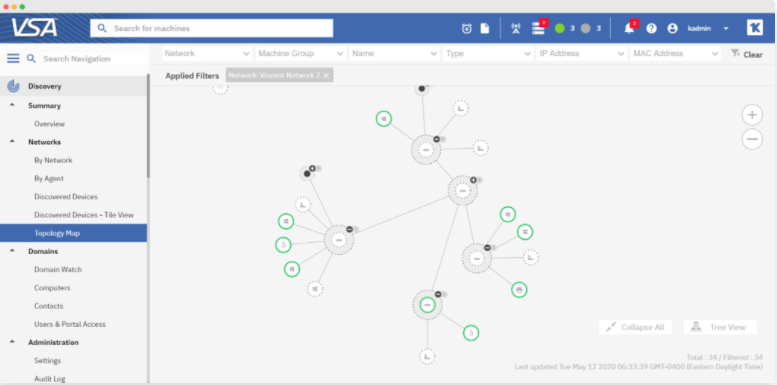
The firm’s software is designed with enterprises and managed service providers (MSPs) in mind, and Kaseya says that over 40,000 organizations worldwide use at least one Kaseya software solution. As a provider of technology to MSPs, which serve other companies, Kaseya is central to a wider software supply chain.
The attack on Kaseya :
According to the cybersecurity firm that conducted the investigation they reported that Huntress has tracked 30 MSPs involved in the breach and believes with “High Confidence” that the attack was triggered via an authentication bypass vulnerability in the Kaseya VSA web interface.
As per the information provided by the cybersecurity firm, this scenario allowed the attackers to circumvent authentication controls, gain an authentication session, upload a malicious payload, and execute commands via SQL injection, achieving code execution.
The REvil ransomware was deployed as a fake update – it was deployed across the estate – including on MSP client customer’s systems.
The Company reported that it took measures to prevent the spread of any malware. They said they sent notifications to on-premises customers to shut off their VSA servers and the company shut down their VSA SaaS infrastructure.
Below we have given the REvil ransomware execution demo executed by Sophos:
The Recovery actions were taken by Kaseya to overcome the situation as per their SaaS playbook.
Considering the level of threat Kaseya was in, they suggest to shut down the on-premise VSA servers. There could be a chance that these systems are powered off in a state with pending jobs still queued to ransom more downstream endpoints once connectivity is restored.
According to Huntress, it is vitally important to remove these pending jobs prior to re-enabling connectivity.
They released a script to clear out any pending VSA procedures/scripts/jobs that may have accumulated since the shutdown, along with a “VSA SQL Audit Report” tool.